Risk Management
Basic Approach
We are promoting the development and operation of Group-wide systems that enable us not only to identify and prevent latent risks, but also to respond rapidly to and deal with risks that have already manifested themselves.
Risk Management System
We have established a Risk Management Committee responsible for building and managing a Group-wide risk management system under the umbrella of the CSR Conference, our highest decision-making body regarding CSR. The committee is advancing the development and management of a Group-wide system to work on identifying and preventing potential risks and to swiftly respond to and resolve materialized risks.
Additionally, each committee reports to the CSR Conference on the status of its activities and future plans regarding its control activities related to the risks within its jurisdiction.
Individual risks that have materialized are handled by the committee or department in charge of that risk, and are reported to the Risk Management Committee, including the status of implementing recurrence prevention measures and horizontal rollout.
The Risk Management Committee monitors whether risk management within Zeon Group is appropriately controlled and prepares a Group-wide risk list. Based on the list, the committee reports on control activities related to Group-wide critical risks to the CSR Conference and the Board of Directors to confirm risk management effectiveness.
Moreover, each organization within Zeon Group prepares its own list of risks, recognizes risks specific to that organization along with Group-wide risks, and implements any control activities needed based on the recognition. Evaluations and control activities for these individual risks are compiled by the Risk Management Committee and shared with the individual committees and departments they fall under, thereby increasing the effectiveness of Group-wide risk management activities.
Group-wide risks include those related to climate change and human rights, among others.
BCP Formulation and Training
Recognizing the need on business continuity to minimize the impact of damage from disasters such as earthquakes and severe storm and flood damage, we have formulated a Business Continuity Plan (BCP), and we implement training to enhance its effectiveness. In FY2024, we conducted two whole-company emergency headquarters drills, one whole-company emergency headquarters secretariat drill, and two plant drills. Through these drills and other activities, we ensure the effectiveness of our BCP and work to strengthen our resilience to disasters.
In addition, each individual business division and plant has formulated its own BCP, and has put in place systems to facilitate a rapid response in the event of an emergency. We are also implementing Business Continuity Management (BCM) to maintain and strengthen our BCP and its effectiveness through ongoing improvement and our unique training.
Whistleblowing System
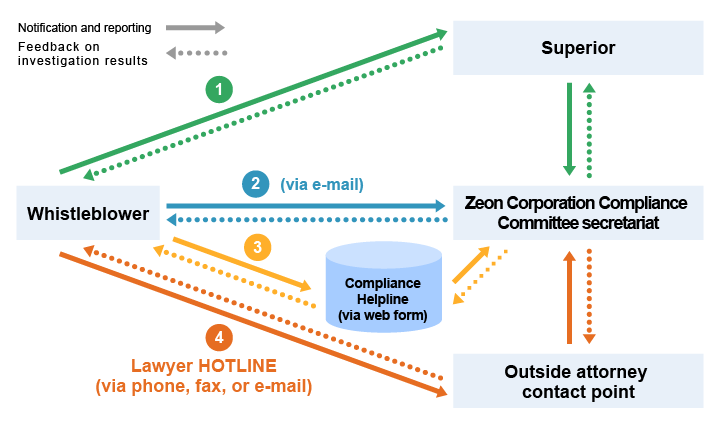
We have put in place a confidential whistleblowing system to identify information about potential risks as early as possible so that appropriate action can be taken. Reporting channels for risk information include internal channels such as reporting through superiors and reporting directly to the Compliance Committee secretariat. We have also set up the web-based Compliance Helpline, which allows anonymous reporting. In addition, we have established the Lawyer HOTLINE, with an outside attorney serving as the contact point, broadening the options available to whistleblowers (1 to 4 in the flowchart).
This whistleblowing system accepts reports related to overall compliance, including harassment, human rights violations, corruption and bribery, theft, fraud, threats, insider trading, and information security issues.
Upon receiving a report, the Compliance Committee secretariat investigates the facts regarding the report, while giving the utmost consideration to the privacy of the whistleblower and maintaining confidentiality, and, based on the results, takes appropriate actions such as instructing relevant internal departments to implement countermeasures.
We also ensure that employees are informed of the purpose of the system and that whistleblowers who make reports in good faith will not be subject to dismissal, reassignment, discrimination, or any other disadvantageous treatment as a result of their report.
Information Security System
We recognize that cyber-related incidents constitute one of the risks that may impede business operations. To ensure business continuity and growth and to maintain social trust, we are committed to securing the digital environment, including information systems and industrial control systems.
Under the leadership of senior management, all directors, officers, and employees, together with our business partners, will address the expectations of diverse stakeholders and promote initiatives based on the following policy in order to establish and maintain a resilient cybersecurity framework.
- 1Management Responsibility and Governance Structure
We position cybersecurity as a key management priority. Senior management will take the lead in implementing risk-based measures. We will establish a company-wide framework and promote coordinated efforts across relevant departments.
- 2Securing Resources and Human Resource Development
We will secure the necessary personnel, technologies, and budget to continuously strengthen our cybersecurity measures. Through education and awareness programs for employees and related parties, we will promote improvements in awareness and capabilities.
- 3Risk Management and Incident Response
We will conduct periodic risk assessments and implement measures according to the level of risk. In the event of an incident, we will respond promptly to minimize damage, ensure early recovery, and prevent recurrence.
- 4Supply Chain and External Collaboration
We will collaborate with Group companies and business partners to ensure security throughout the supply chain. We will also strengthen our measures by leveraging the latest information through cooperation with specialized institutions and industry associations.
- 5Factory Cybersecurity
Particularly at manufacturing sites, we will implement cybersecurity measures with a strong emphasis on preventing disasters, including explosions and fires caused by high-pressure gases and large-scale leaks of toxic gases.
- 6Continuous Improvement
Through monitoring and internal audits, we will periodically evaluate the status of our initiatives and pursue continuous improvement in cybersecurity.
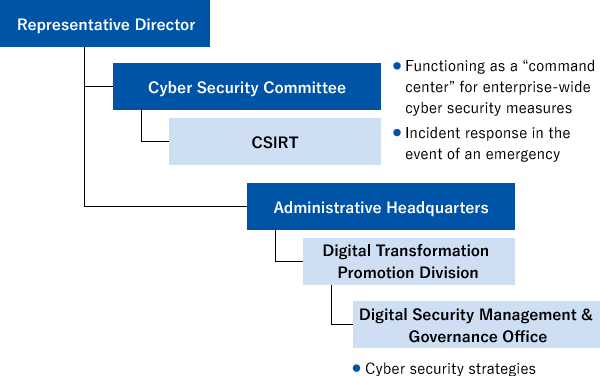
Structure and System
As part of our efforts to strengthen and promote information Systems relating to cyber security risk security, we have established a Cyber Security Committee, which reports directly to the representative director. The Committee is responsible for providing guidance, monitoring, and assessment of cyber security measures on an enterprise- wide basis. It is also positioned as the governing body for The Risk Management Committee performs monitoring to determine whether risk management in Zeon Group is directed properly, compiles a list of risks covering the whole enterprise, reports to the CSR Conference and Board of Directors on control activities relating to Group-wide risk management, and confirms the effectiveness of risk management. Moreover, each Zeon Group organization creates its own list of risks, recognizes risks specific to that organization along with Group-wide risks, and implements any control activities needed based on the recognition. Individual risk evaluation and control activities are compiled by the Risk Management Committee and shared with the individual committees and departments they fall under, thereby increasing the effectiveness of Group-wide risk management activities. Group-wide risks also include those related to climate change and human rights. rapid and effective incident response during emergencies. In addition, a Computer Security Incident Response Team (CSIRT) has been established, which reports to the Committee, and which is responsible for making expert judgements and implementing a practical response in the event of a security incident. The CSIRT is tasked with implementing an appropriate, speedy response if an incident occurs at any Zeon Group company. In addition, in order to respond to today’s increas ingly complex and diversified cyber-attack threats, the CSIRT is working to realize ongoing improvement of Zeon’s ability to respond to cyber security incidents, proceeding with a step-by-step enhancement of this capability, and collaborating with external organizations where necessary.
Major Initiatives
Zeon has established specialist units to handle matters relating to cyber security, and we are implementing the following types of measures. Cyber security risks are being transformed by the continuing evolution of digital technology and the widespread promotion of DX. We recognize that implementing a strategic, effective response to these risks is an important management issue for Zeon, and going forward we will be working to strengthen our initiatives in this area and realize ongoing improvement.
| Technical and organizational measures | Human resources measures |
|---|---|
|
|
